#RabbitHole: @okias@floss.social is doing a lot work to mainstream #sdm845 patches to the #linux kernel. During a meeting of Phosh.mobi e.V. members I learned that there seem to be not many testers for #Shift6mq #axolotl. I still had a broken Axolotl sitting on my desk…
- repaired the phone that originally had been bought as part of a #ShiftPhone8 deal
- cleaning inside (residue from water contact)
- new display (two lines of broken pixels)
- new usb-c pcb (didn't charge, data broke during testing)
- learned about
edlto recover if phone wouldn't boot to fastboot anymore (yes, really had that situation later)
- learned about the difference of fastboot and fastbootd mode
- learned about u-boot and the boot chain on the phone
- learned about dynamic partitions used in Android and how to use them from #linux
- learned about
pmbootstrap- to build my own device images (mixture of existing
axolotlandsdm845to be compatible to the phone and the usage with u-boot and dynamic partitions) - changed pmbootstrap to build small (92M) boot image for boot_a/b partition
- to build my own device images (mixture of existing
- tried to get more space for out of the phone for boot & root than provided by boot_a/b and system_a/b
- resized userdata of Android
- created two additional partitions for postmarketOS
- learned how to recover from kernel not booting without re-flashing
- learned how to compile a kernel using
./envkernel.shand pmbootstrap
Now I'm quite sure I can recover from any failure I will encounter while testing sdm845 kernels and I have the following setup on my Shift6mq:
- ShiftOS-L with small userdata partition in slot_b
- applications for demoing the phone installed
- work profile to contain closed source applications
- postmarketOS edge installed on partitions behind userdata
- u-boot on rescue_a
- 1GB pmOS_boot
- 60GB pmOS_root
- applications for demoing
- multi-user: my testing user, demo user
- everything except cameras work
- dual-boot possible on-the-go: enter fastboot (by holding vol-up at start), change slot, reboot
I put my notes on the postmarketOS wiki.
I started two merge requests:
- support audio configuration when started through u-boot in alsa
- add support for booting using u-boot and dynamic partitions to axolotl
I'll carry the phone at #clt2026 - Chemnitzer Linux Tage 2026 - on saturday 28th this month. I'll mostly be around the "Linux on Mobile" booth.
On my testing #Librem5 running #Mobian I had obviously installed a workaround to get echo cancellation for calls by using #pulseaudio for audio. I had forgotten about it and after some update or hardware tinkering sound just didn't work anymore.
I found out that I knew not much about sound and while trying to understand how it is supposed to work I wrote some of my findings on the Librem5 community wiki.
I'd be thankful for corrections and additions to be able to move the page soon out of the work in progress section.
Uhm, that's a question about personal background - I guess. The only thing I miss is #osmand, but I know I could invest time and replace most of the functionality I use by #brouter and #brouterweb and #PureMaps.
But
- I reject banking apps of any kind and prefer the safety of ChipTan or HBCI (offered by @glsbank@ruhr.social and by #sparkasse)
- I don't care about any closed source service
- I'm able to run matrix bridges to relay to any network I'd need for work or family life
- I do not use my phones smart capabilities much (beside running #fractal for my matrix account to communicate with my family)
Yes, sometimes I'm catching myself looking at some page using firefox, scrolling through some fediverse posts using #tuba.
If I really need to use the #Librem5 I usually knew in advance and carry a lapdock to use its convergence feature and then it is mostly like a notebook.
I do not miss anything even though there is potential for nice improvements.
@ati1@mastodon.social @ananas@scicomm.xyz @agx@ruhr.social @opensourceopenmind@vivaldi.net
lack of [...] apps
There is no such lack, but you need to be willing to give up the apps you know from Android (or keep using part of the evil empires products by tinkering with #waydroid or #atl - android translation layer).
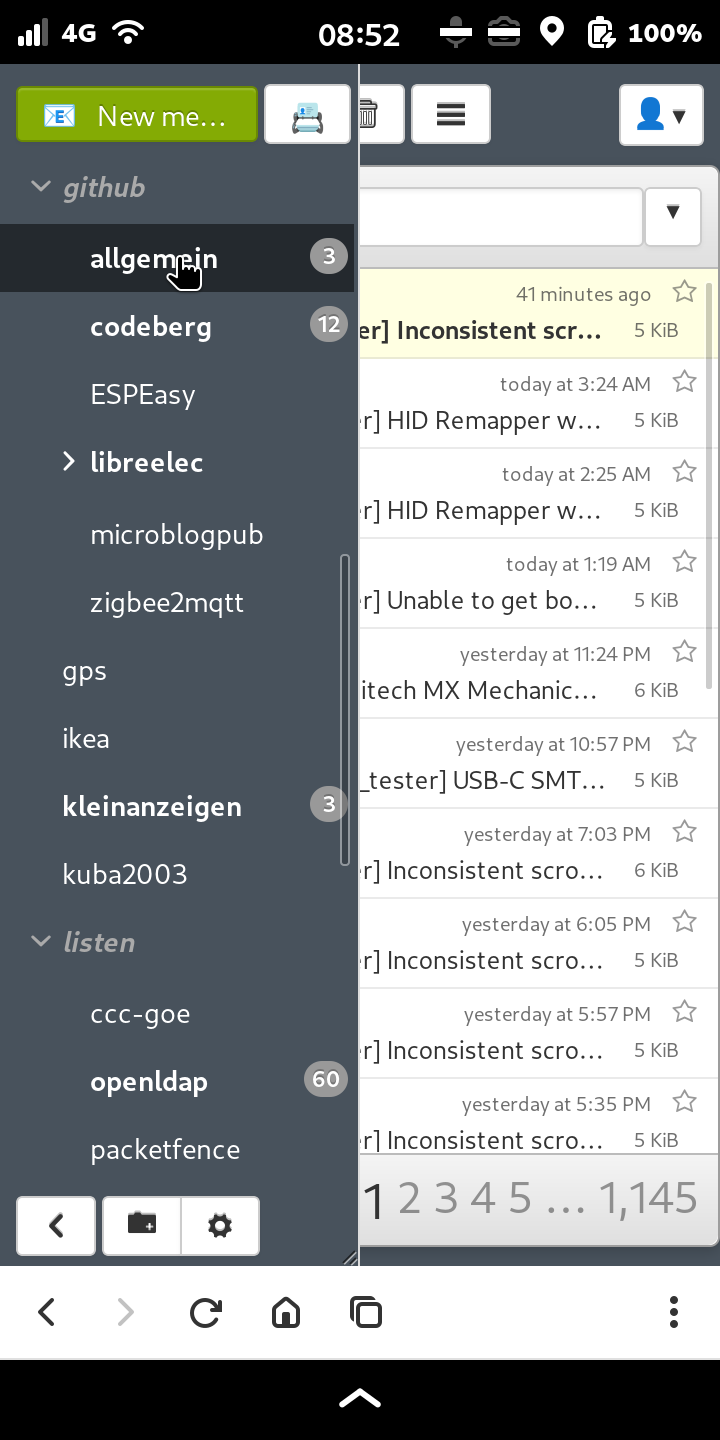
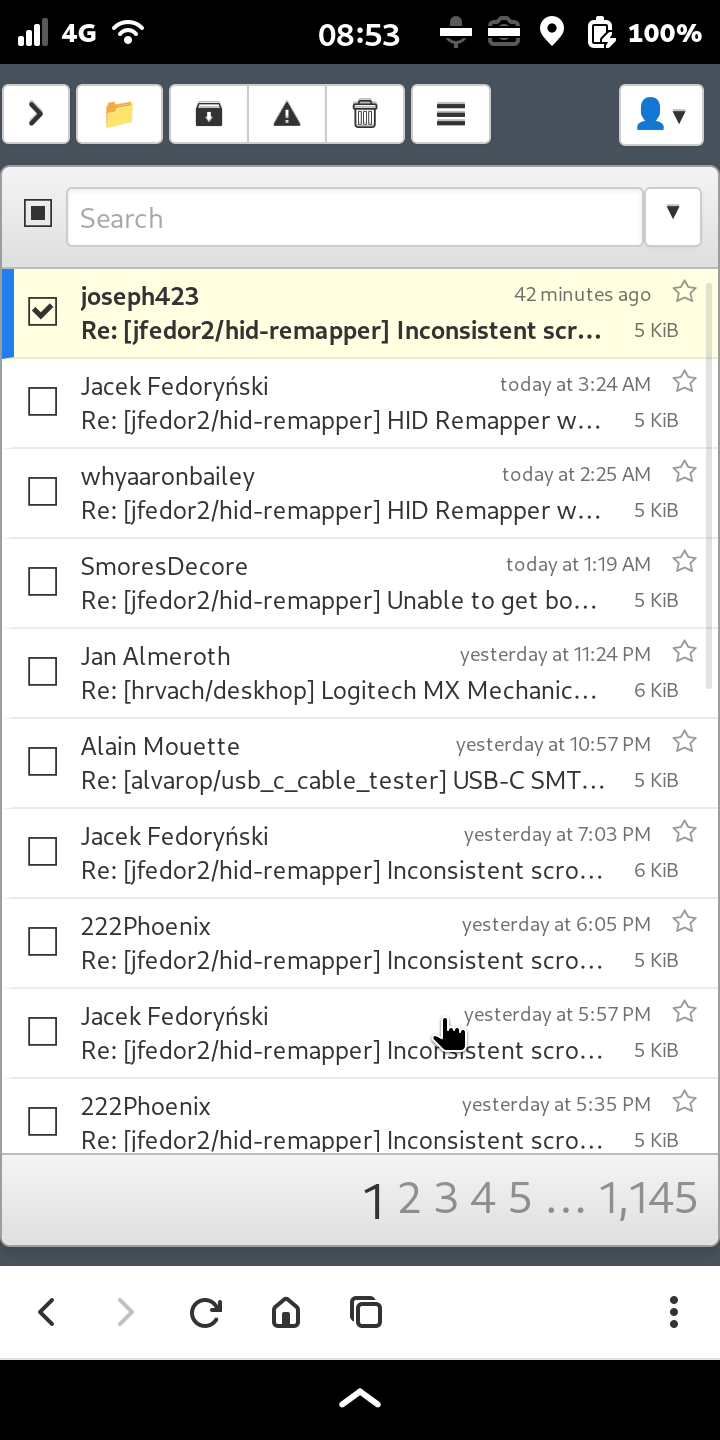
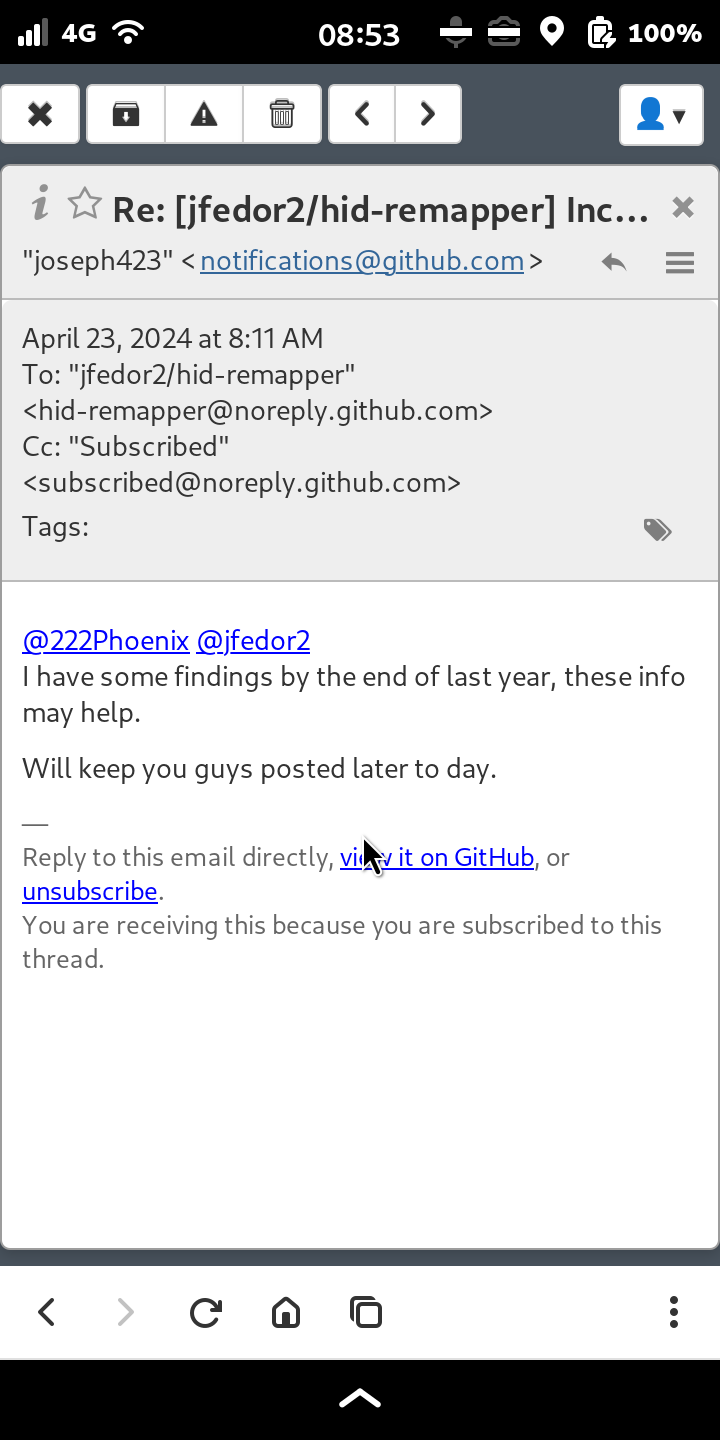
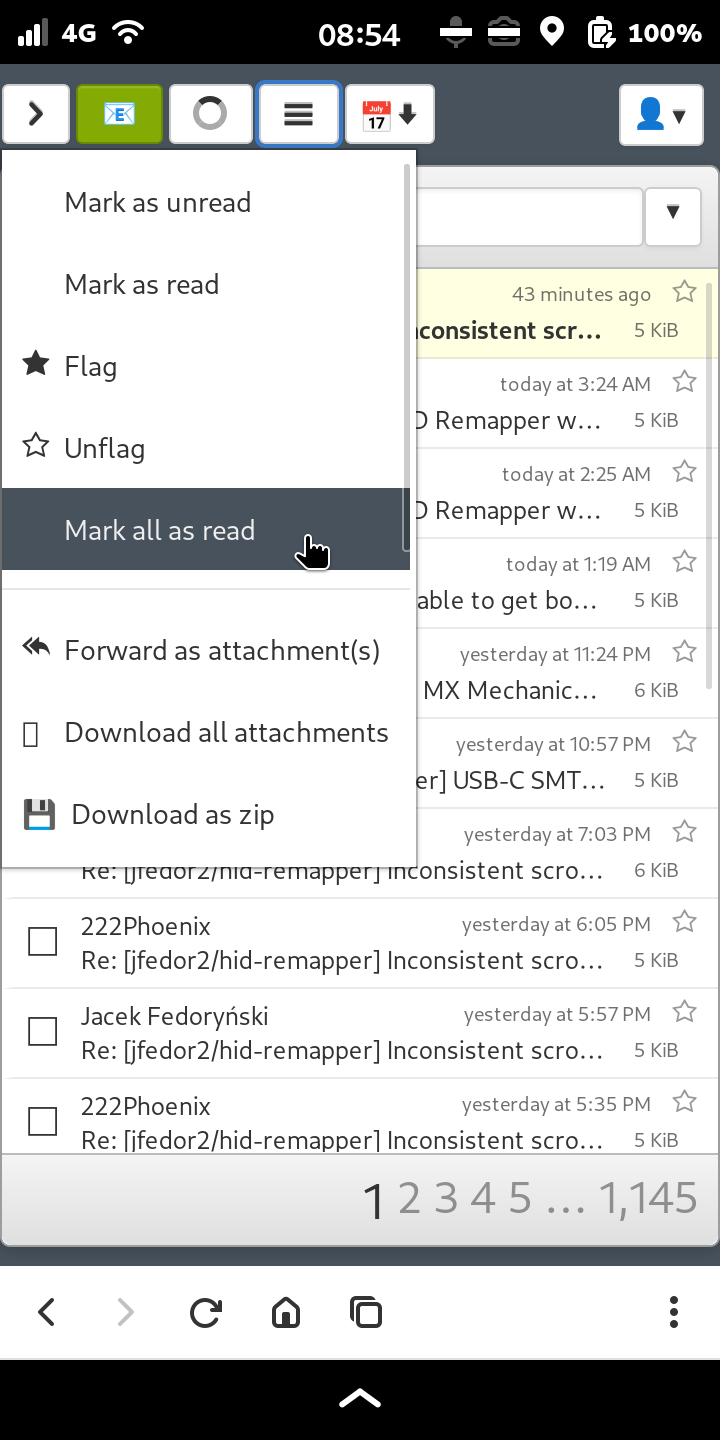
There are other apps to discover. I had to completely start over finding out which apps I want and which ones to use. For E-Mail e.g. I'm using a self-hosted #snappymail in #tangram, because I couldn't find any app I liked.
The only thing I'm still missing is #osmand - one of two reasons my tablet is running on #LineageOS. The other reason is that I didn't come across a good tablet hardware made for linux containing an 4G/5G modem.
Or do people still order new ones at $800?
Looking for a OpenPGPcard in FLOSS Shop I came across this offer:
https://www.floss-shop.de/de/elektronik/geraete/78/librem5-mobil-phone
This completely went by me - it's possible to order a #Librem5 in Europe?!
Also would you reveal what bank you use?
Well, I own my own bank - at least partly - a very small part of it actually. @glsbank@ruhr.social offers to use ChipTAN.
I'm using this device as a second factor which together with the needed banking card really offers a second factor and is not just another software running on the same smartphone.
For paying online I use "Lastschrift" if not outsourced to PayPal (which I stopped using years ago), a bank transfer for smaller sums or sometimes the credit card which I have to confirm sometimes using an SMS TAN and some secret phrase. Generally I use my notebook if I do such stuff and only used my Librem5 very few times when my notebook has not been around.
It is the most secure solution beside HBCI which you could use with GLS bank also if you kindly ask them.
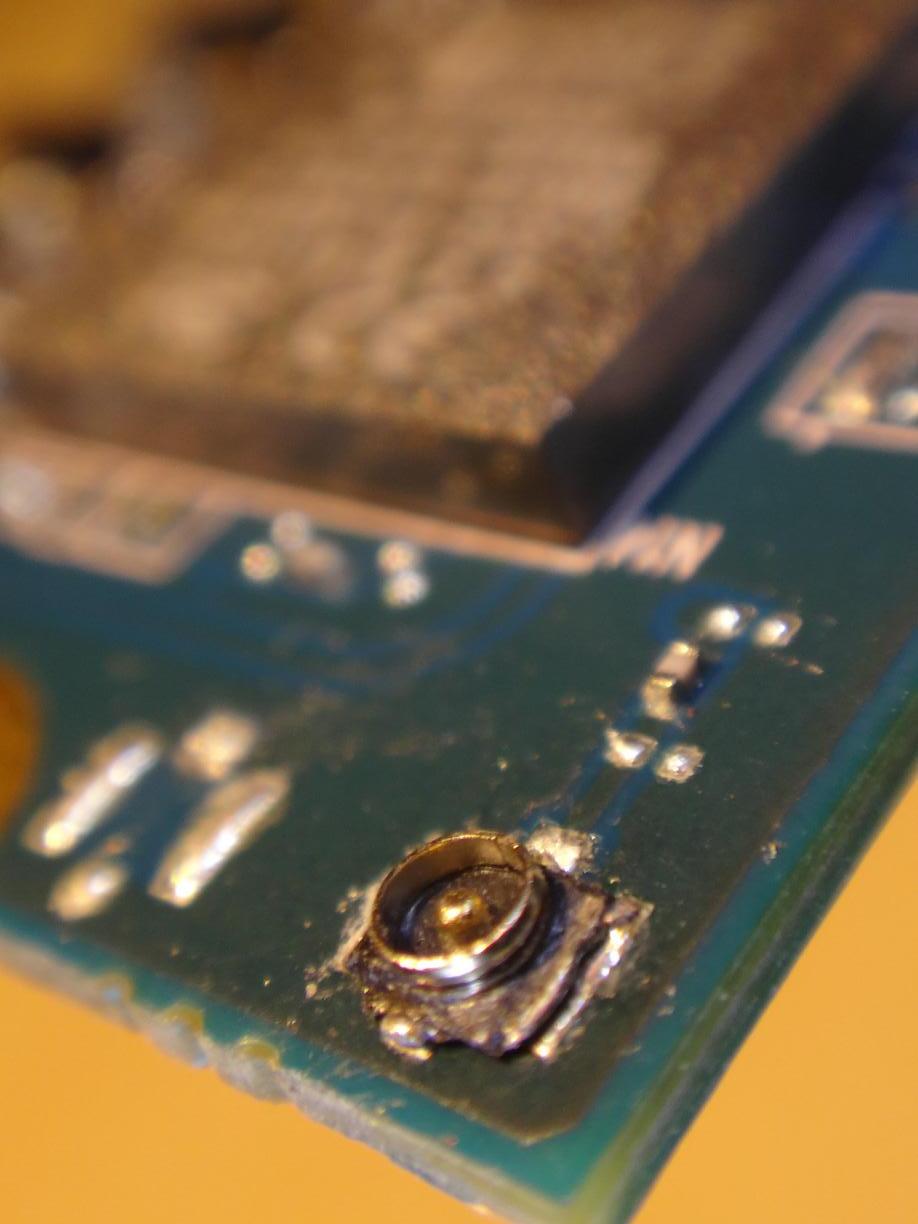
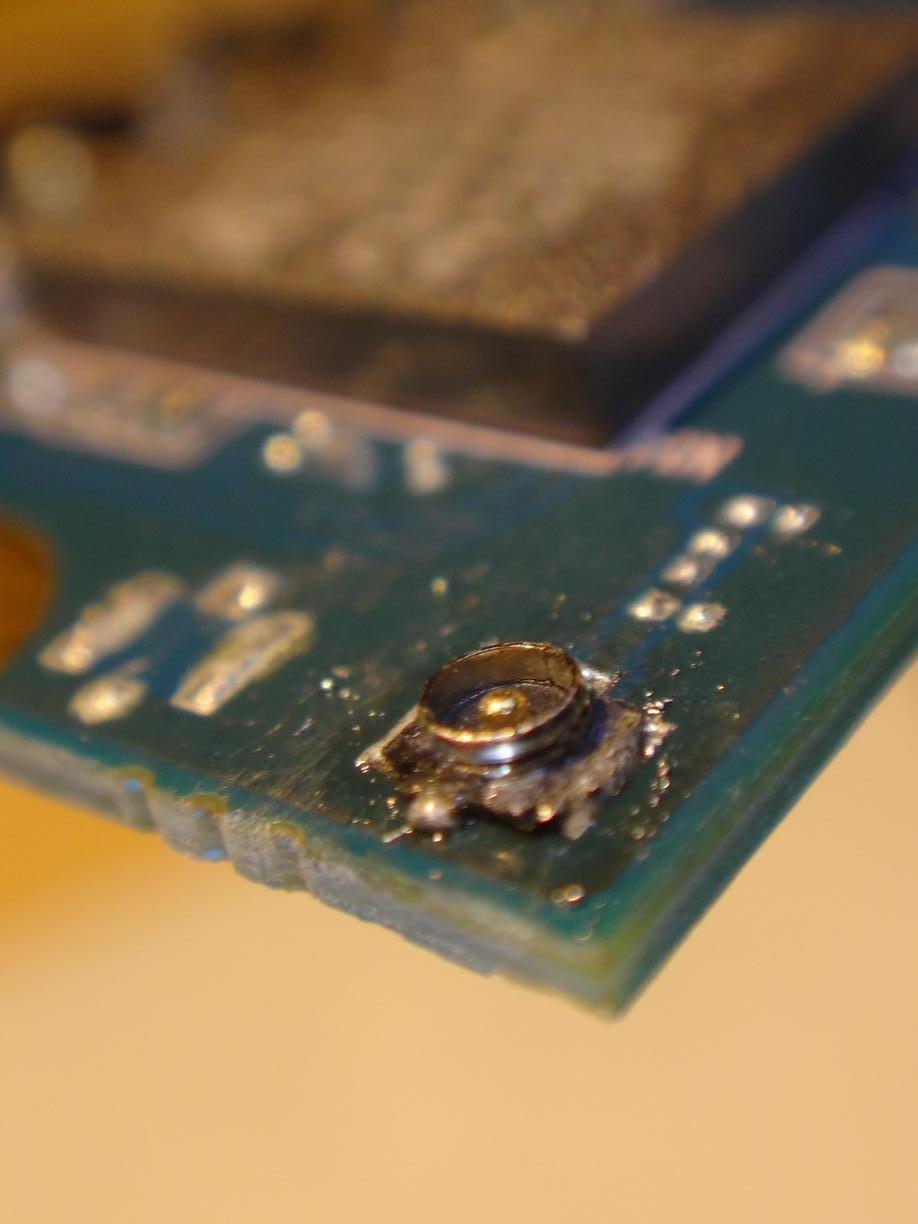
After some searching and reading I bought a heat gun to repair the damage I did to the modem of my #Librem5 when I changed its broken middle frame.
First tries tonight went well I think. I removed and re-soldered one of the antenna sockets of my unused redpine wifi/bt card for practicing.
First picture shows the socket removed and soldered to the pcb again without removing any solder or adding new one.
The second picture shows the socket after de-soldering the socket a second time, cleaning the pcb with some de-soldering braid applying some soldering paste and soldering it back on.
Thanks @z3r0fox@mastodon.social for the hot tip !
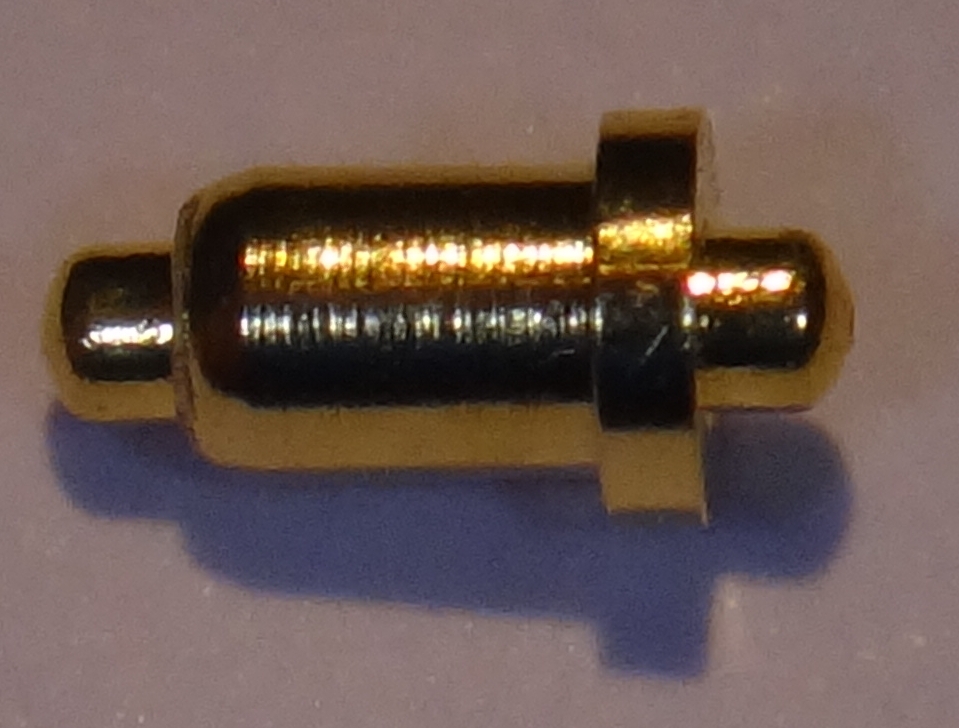
Repairing my #Librem5 I found again a pogo pin that fell out of the middle frame and thought I'd offer them on my #flohmarkt - just in case someone lost one.
Just donated to the effort to improve sound quality on the #Librem5 when using #pipewire: https://opencollective.com/dephcom/projects/pipewire-echo
I'd be even more happy about the approach of sponsoring development through the community if this donation would be accepted as being for an official non-profit organization accepted as such in Germany.
Giving for #OpenSource should be respected as a a benefit to the public and appreciated by the government by whatever means they do this for other purposes (in Germany it's possible to declare such donations for reducing taxes to pay).
Hey #MobileLinux community - if everybody gives a little there'll be a fair pay for someone doing this work.
Due to the discussion around #deepseek and the #privacy aspects of using it I read about #KeystrokeDynamics.
Imagine - each time you fill a form on the some website you're actually leaving fingerprints on it by the way you type. If the site reads your keyboard through a websocket connection and thereby knows the rhythm you have clicking your single keys, the time you hold down each key and the pauses you make thinking, this is a biometric that might even reveal the mood you're in.
There's tons of literature out there about various aspects of using keystroke dynamics.
I'm using a #deskhop* to connect my keyboard and mouse to my notebook and #Librem5 mobile phone to use both seamless like a multi-monitor setup.
Reading about a failed indiegogo campaign to build a usb device changing the metrics of typing in a way to cloak keystroke dynamics I had the idea that this maybe could be an extension to deskhops functionality.
Clear sky, no #clouds.
Copying the image from one #Librem5 to another #Librem5.
Stars shining, just me my notebook and two usb connections.
#Freedom, #sovereignty and no other peoples computers.
In my post about waking my #Librem5 by calling to receive matrix messages I forgot to mention one of the actors: #PhoshAntiSpam.
PhoshAntiSpam rejects or silences incoming calls depending on a text file containing phone numbers and/or your address book.
If you're using #Phosh on your mobile phone and you get calls you do not want, it'll be of great help. Shoutout to @kop316@fosstodon.org
Waking my #Librem5 from suspend when a new #matrix message triggers a notification.
Starring:
- matrix server: #conduit
- #UnifiedPush and notification server: #ntfy
- #sip client: #pjsua
- #fractal: matrix client
- #feedbackd: rhythm & sound
Note to myself: if you play with sound-themes on your #Librem5 (and probably any other #MobileLinux device) and you seem to be stuck with the default sound theme (freedesktop) then delete ~/.cache/event-sound-cache.tdb* and restart #feedbackd.
Thanks to @agx@librem.one for helping me on matrix:community-librem5 and for the great software!
Receiving SMS plays a long tune on my #Librem5. For a few persons I'd like to have this tune played also if they send me a message using #matrix.
A problem is that the #fractal flatpak does not use #feedbackd yet to signal new messages and on #PureOS #Byzantium there's no way to define different sounds for different notification events.
So I started testing a small script to read notifications and trigger feedback for messages coming from an account containing some string:
#!/usr/bin/python3 import gi import time gi.require_version('Lfb', '0.0') from gi.repository import Lfb from gi.repository import GLib import dbus from dbus.mainloop.glib import DBusGMainLoop def print_notification(bus, message): keys = ["app_name", "replaces_id", "app_icon", "summary", "body", "actions", "hints", "expire_timeout"] args = message.get_args_list() if len(args) == 8: notification = dict([(keys[i], args[i]) for i in range(8)]) if "account_i_want_to_be_notified_for_like_it_would_be_sms" in notification["summary"]: print( notification["summary"], ': ', notification["body"] ) event.trigger_feedback() Lfb.init('org.sigxcpu.lfbexample') event = Lfb.Event.new('message-new-sms') loop = DBusGMainLoop(set_as_default=True) session_bus = dbus.SessionBus() session_bus.add_match_string("type='method_call',interface='org.freedesktop.Notifications',member='Notify',eavesdrop=true") session_bus.add_message_filter(print_notification) GLib.MainLoop().run()
Problem: using calendar on my #Librem5 running #PureOS Byzantiu once in a while I can't add new appointments anymore and the calendar doesn't sync with my #nextcloud.
A simple goa-daemon --replace solved the problem when it occured. I automated this reading the error shown in the journal when the problem starts.
I made a workaround to monitor and replace the goa-daemon:
Story is probably not new: using a #Librem5 (linux mobile) and everybody insists on using WhatsApp. I didn't care. But all activities the kids want to take part: #WhatsApp.
I could try to evangelize all these football trainers, parents representatives at schools, parents of friends to use something that I'm able to use on my linux phone, but I can't: lack of energy, lack of time, lack of alternatives with the same feature set and stability.
Got out an old Sony Z1 running #CarbonROM. Really old software. Got an so far unused SIM. I used Aurora Store from F-Droid to install WhatsApp from the Google Store on that Android. Registered to WhatsApp and it worked fine sending one test message that never arrived, because the other side didn't have my phone number in their contacts (I guess).
I installed #conduit as a #matrix server on my #yunohost and put mautrix-whatsapp #bridge on its own system using the latest docker image following the documentation to get a minimum configuration running.
Yeah, works. Coupled WhatsApp on the Android Z1 with the bridge and send two test messages resulting in This account can no longer use WhatsApp due to spam shown on the #Android device.
Is that most likely because of my 10+ years device + rooted + Magisk + fake google app store #Aurora or is it something others are experiencing when trying to use the bridge with of the shelf devices, too?
My plan has been to run an independent phone number for WhatsApp on a device that only has contacts for WhatsApp in its phone book and make it available to family members through matrix.
Our participation in society relies in many aspects on the goodwill of a few monopolistic companies that we depend on. They write the rules which device (Android or iOS) and which software (only their own doing whatever they program it to do) we're supposed to use. They train the algorithms that can cut you off our participation.
I wouldn't care the least. I'd even smile when reading this thinking that it's exactly what people supporting companies like facebook/whatsapp deserve. But if the participation of my kids in society is at stake (and not my own which I well can organize without any messenger) it makes me sad.
Hey @usia@fosstodon.org, thanks for the hint. I might try it again sometimes.
I've got one problem with thunderbird though that might be worse when running on a small computer like the #Librem5:
It eats a lot of resources when there's are a lot of messages and folders on the imap server.
I wrote about it here.
That looks really great! Can't wait see it filled with life.
Meanwhile I'll share my solution. I'm an #email user since more than 30 years and I'm running my own email server since nearly the start of it.
The lack of having a reliable email client for my #Librem5, my sons #pinephone and #MobileLinux in general bothered me a long time. #Geary didn't fit my needs and #Thunderbird which I use on my desktop is no option for mobile devices, yet.
I ended up using #tangram to access a #selfhosted #snappymail.
Yes!
On an unencrypted registration SSID authorized a client through a portal page.
Then showed the client via dpsk (dynamic pre-shared key) provisioner login data for the encrypted SSID to connect to a network with internet access.
When the client connects to the unencrypted SSID it gets redirected to a portal to enter an email address (and possibly other data). Packetfence sends an email to a pre-configured address (owned by the sponsor) containing a link to approve the request for access.
The client waits on a portal html page for the sponsor to click the link. After the sponsor clicks the link to approve the request the clients web page reloads and shows the name of the encrypted SSID to connect to and a password for the connection.
Next step to accomplish: configure OpenWRT (hostapd) and Packetfence to allow the usage of the PSK to connect to the encrypted SSID.
BTW: Testing this I'm using #deskhop to switch seamlessly between my notebook and my #Librem5 which I use as a test client for the wifi connection to the OpenWRT access point.
I'm not really a friend of being disturbed by notifications. My #Librem5 does only play sounds on SMS. Anyway...
What I've been thinking of especially since there is some work on the linux system of the #Pinephones Modem is if there wouldn't be a way to implement some service into the modem that does work even when the phone is in suspend mode.
This wouldn't solve the quest of having some service providint push notification, but it would solve the problem first that on the Librem5 and the Pinephone push notifications can't be received while the phone is suspended.
Another way to get this without having to hack on the modem would be to run a service that would actually voice call a phone when it's supposed to get a notification to wake it from suspend. This solution could be illegal in some jurisdication, because you signal something by a call that is not intended to be taken (and thereby charged).
After a wake-up from suspend by whatever dedicated method the linux system could do whatever would be good to get information about the event that initiated the wake-up call/[wake on modem data thingy].
From there whatever happens in linux could evolve. At first on the phone side I thought one would wait for the services defined by the user to connect to their servers and exchange informations. But this could also evolve into some protocol where the phone asks at the wake-up service for the reason for the wake-up and just make sure that it acts upon that information.
Maybe I misunderstood the whole situation and the whole problem, but it's nice that you started the discussion about this topic and I'd love to learn more about other ideas.